REMOTEKILL®
Deauthorize at-risk devices and data
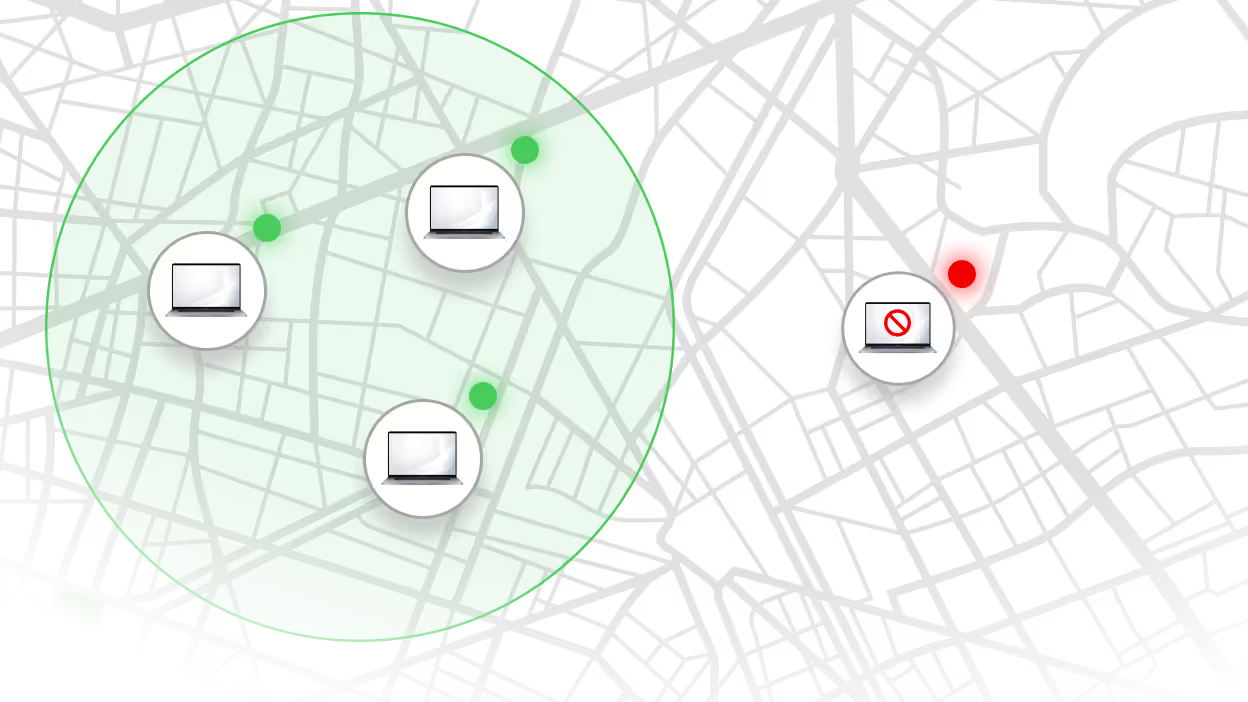
Respond to any security incident with powerful countermeasures. Lock down lost or stolen devices on-demand or via predefined triggers. Freeze sensitive data with emergency encryption and deauthorize devices with OS lockout.